In the early hours after the towers fell in New York and the smoke drifted across the skyline of Washington, a new kind of war quietly began. It did not start with tanks rolling across borders. It did not begin with aircraft formations darkening the sky. Instead, it began in dimly lit intelligence rooms where analysts stared at fragments of information scattered across thousands of screens.
On September 11th, 2001, the United States faced an enemy unlike any it had confronted before. The attacks had been coordinated across continents, planned in secrecy, and executed by individuals who vanished back into the shadows the moment the destruction was done. Behind the operation stood a network, a decentralized organization built on secrecy, loyalty, and ideology.
At its center was a name that would soon become known across the world. Osama bin Laden. The organization he led, Al-Qaeda, had spent years constructing a web of fighters, financiers, facilitators, and safe houses stretching across multiple countries. Its leaders operated from remote training camps. Its operatives moved quietly between borders, and its communications traveled through channels designed to leave almost no trace.
But after the attacks, everything changed. Within days, the United States government launched a global campaign to dismantle the organization responsible. Military forces prepared for war in Afghanistan, where al-Qaeda had built its primary sanctuary. Yet, even before the first bombs fell, another effort had already begun, a quieter campaign.
One fought not on open battlefields, but within the hidden world of intelligence. At the center of that campaign stood the Central Intelligence Agency. Its mission was simple in concept but almost impossibly difficult in execution. Find the leaders of al-Qaeda, track them, understand how the network functioned, and ultimately help dismantle it piece by piece.

But the moment American forces entered Afghanistan, the enemy began to disappear. Training camps were abandoned. Safe houses were emptied overnight. Senior figures within the organization scattered in every direction. Some fled into the harsh mountains of eastern Afghanistan, hiding in valleys where surveillance aircraft struggled to see and satellite signals faded among jagged ridge lines.
Others crossed the border into Pakistan, blending into the complex landscape of tribal regions where outsiders rarely ventured and loyalties were often impossible to predict. Within weeks, the leadership of al-Qaeda had dissolved into fragments spread across multiple countries. To the outside world, it appeared as if they had vanished.
But intelligence officers knew something critical. Networks do not simply disappear. They adapt. Every organization, even one built on secrecy, must communicate, move money, deliver messages, and coordinate actions. And each of those activities leaves traces. Tiny fragments of evidence. A phone call placed from the wrong village.
A courier seen traveling between two remote towns. A financial transfer that connects individuals who should never appear on the same ledger. Individually, these clues meant almost nothing. But together, they formed patterns. inside CIA headquarters and intelligence centers around the world. Analysts began collecting those patterns.
They examined intercepted communications, financial data, documents recovered during military operations, and reports from sources scattered across multiple regions. Every fragment was fed into a growing analytical effort designed to answer one question. Where were the leaders of al-Qaeda hiding? But this was not a conventional manhunt.
Many of the individuals being tracked had already learned from years of experience how to evade surveillance. They avoided electronic communications. They changed locations frequently. They relied on trusted intermediaries to carry messages rather than using telephones or radios. To find them would require more than technology.
It would require building a map of an invisible network. And somewhere within that network were the pathways that connected the scattered pieces of al-Qaeda’s leadership. The challenge facing the intelligence community was enormous. They were trying to locate men who rarely appeared in public, who communicated through layers of secrecy, and who were protected by terrain, distance, and loyal supporters.
But intelligence officers understood something else. Every hidden system, no matter how careful, has a point where information must move. A message must travel. An instruction must reach a fighter. A courier must carry words from one leader to another. And if those movements could be identified, the entire structure might begin to reveal itself.
But this was only the beginning of the hunt. Because somewhere inside that invisible web of couriers, messages, and hidden relationships was a pathway leading directly to the leadership of al-Qaeda. And discovering that pathway would become one of the most complex Intelligence operations of the modern era. As American military operations expanded across Afghanistan in late 2001, the physical battlefield began to shift rapidly. Cities fell.
Training camps were destroyed. Entire compounds that once housed hundreds of fighters were reduced to rubble within weeks. Yet, the most important targets were no longer there. The senior leadership of al-Qaeda had already begun moving long before many of the bombing campaigns intensified. The organization had anticipated the possibility of retaliation after the attacks of September 11th.
Plans for dispersal had quietly existed for years. Safe routes had been identified. Mountain passages had been mapped. Contacts had been established across borders. When pressure finally came, the leadership did not attempt to defend fixed positions. Instead, they dissolved into the landscape. Some slipped into the towering mountains of eastern Afghanistan, where narrow valleys and isolated villages created a natural maze difficult for any army to navigate.
Others crossed the poorest border into Pakistan’s tribal regions, areas where central authority was limited and local networks of loyalty often outweighed national laws. From the outside, the organization appeared shattered. But intelligence analysts knew the truth was more complicated. The fighters might scatter. The camps might vanish.
But the leadership still needed to communicate. And communication meant structure. Inside intelligence centers, analysts began reconstructing that structure from fragments. Every intercepted message, every financial transfer, every recovered document became a potential clue. They were not simply looking for locations.
They were trying to understand relationships. Who spoke to whom? Who carried messages? Who handled money? Who served as the invisible connectors between senior leaders and operational cells. The work resembled assembling a massive puzzle without knowing what the final picture should look like.
Thousands of pieces, most of them incomplete, some deliberately misleading, but patterns slowly began to emerge. Analysts noticed that even highly secretive organizations depended on intermediaries. Senior leaders rarely communicated directly with fighters on the ground. Instead, messages moved through trusted individuals who acted as bridges between different layers of the network.
These individuals were rarely famous. Their names seldom appeared in public reports. But within the structure of al-Qaeda, they played a crucial role. They were the couriers. And in the hidden architecture of a clandestine organization, couriers were often more valuable than commanders because they knew where the commanders were.

But this discovery created a new challenge. Tracking a courier in the mountains of Afghanistan or the tribal areas of Pakistan was far more difficult than monitoring a phone call or intercepting a radio signal. Most couriers traveled quietly. They used vehicles that blended into local traffic.
They carried no obvious identification and many operated in regions where surveillance was extremely limited. So the intelligence effort expanded beyond electronic monitoring. Field officers were deployed across multiple countries to build networks of human sources. Some worked through local security services.
Others developed contacts among tribal groups, businessmen, or travelers who might notice unusual patterns of movement. Information gathered from these sources was often small and seemingly insignificant. A stranger visiting a remote village. a vehicle appearing repeatedly along the same isolated road, a messenger traveling between towns that had no obvious connection.
Individually, these observations meant very little. But when combined with other intelligence, they sometimes revealed something important. A pathway, a connection, a recurring route used by individuals who preferred to remain invisible. But this process moved slowly. Weeks could pass with no progress.
A promising lead could vanish overnight when a suspect changed locations or disappeared into a new region. Sometimes an entire trail collapsed after investigators realized they had been following misinformation deliberately planted by members of the network. And this is where the hunt became even more complicated because al-Qaeda’s leadership understood that they were being pursued.
They knew their communications were monitored. They knew their financial movements might be traced, so they adapted. Electronic devices were avoided whenever possible. Telephones were used rarely and often only once before being discarded. Sensitive messages were delivered face to face or carried by trusted couriers traveling long distances through difficult terrain.
In many cases, a courier might not even know the identity of the person sending the message or the individual meant to receive it. Layers of secrecy were built into every exchange. But that secrecy had an unintended consequence. It slowed communication. And whenever communication slows, organizations must rely even more heavily on the few individuals trusted to carry information between leaders.
That meant the couriers became essential. Without them, instructions could not move. Plans could not spread. Operations could not be coordinated. Inside intelligence headquarters, analysts began focusing more attention on identifying these intermediaries. They studied travel records. They examined border crossings.
They reviewed captured documents for names that appeared repeatedly in connection with different members of the organization. Sometimes a name appeared only once. Sometimes it appeared across several unrelated reports and occasionally a name surfaced again and again quietly linking multiple individuals who otherwise seemed unconnected.
Those names drew attention because somewhere among them were the hidden arteries of the network. And if intelligence officers could follow those arteries long enough, they might eventually reach the heart of the organization. But that realization introduced an even deeper mystery. Because the most important leaders of al-Qaeda had seemingly vanished without leaving clear trails behind.
Their communications were rare, their movements unpredictable, their appearances almost non-existent. It was as if they had stepped completely outside the visible world. And yet messages continued to move. Orders continued to travel across borders. Operations continued to be discussed in whispers and fragments, which meant that somewhere unseen and almost silent, the leadership was still guiding the network.
The challenge now was no longer simply finding individuals. The challenge was understanding the hidden system that allowed them to remain invisible. And until that system was uncovered, the most important figures in the organization could remain out of reach indefinitely. But hidden networks have weaknesses, and sooner or later, one of those weaknesses was going to appear.
The deeper analysts looked into the scattered remnants of al-Qaeda’s network, the more they encountered a troubling reality. The organization was still functioning, not openly, not visibly, but beneath the surface, the machinery of communication continued to operate with quiet precision. Messages moved. Orders circulated.
Individuals in distant regions still appeared to receive guidance from figures who had seemingly vanished. Somewhere, hidden behind layers of secrecy, the leadership was still directing parts of the organization. But no one could see how. Inside intelligence centers, frustration slowly grew.
Vast quantities of data had been collected since the beginning of the campaign. Communications intercepts, financial records, travel logs, interrogation reports, capture documents from abandoned compounds. All of it had been poured into analytical systems designed to reveal hidden connections. And yet, the most important question remained unanswered.
Where were the senior leaders of al-Qaeda? Analysts could identify fragments of the organization, small operational cells, regional facilitators, individuals responsible for logistics or financing. But the figures at the very top, those who had orchestrated the attacks and continued to influence the network, remained almost completely invisible.
They had disappeared into silence. But silence itself can become a clue. Because in the world of intelligence analysis, absence often reveals as much as presence. One of the patterns that began to attract attention was the unusual lack of electronic communication among certain high-ranking individuals. Most modern networks, even clandestine ones, leave digital traces.
Phones are used briefly. Emails are sent through temporary accounts. Radios transmit coded messages. But in this case, many senior figures appeared to have eliminated electronic communication almost entirely. They had reverted to older, slower methods, hand carried messages, face-to-face meetings, layers of intermediaries.
At first glance, this seemed to make the task of tracking them nearly impossible. But it also created a paradox. If electronic communication disappeared, then the physical movement of couriers must increase. Somewhere people were traveling between locations carrying instructions, reports, and decisions. And every traveler, no matter how careful, leaves traces.
But that wasn’t the only mystery. Because when analysts mapped the known movements of al-Qaeda operatives across several regions, they noticed something unusual. Certain individuals appeared to maintain contact with multiple parts of the network even though they rarely appeared in intercepted communications. Their names surfaced quietly in interrogation reports.
They appeared in financial records connected to unrelated individuals. Sometimes they were mentioned by local sources who had no knowledge of the larger intelligence effort. Each report alone meant very little. But when these fragments were placed together, they began forming a pattern. These individuals were not commanders.
They were not public leaders. Yet, they appeared again and again in connection with different layers of the organization. They were the connective tissue of the network. And this is where the investigation began to shift direction. Instead of focusing only on the well-known leaders of al-Qaeda, analysts started searching for the people who moved quietly between them.
the couriers because if the leadership had chosen to avoid electronic communication entirely then these couriers had become the lifeline of the entire system. They carried instructions across mountains. They transported messages between countries. They served as the silent bridges linking scattered leaders to fighters operating hundreds or even thousands of kilometers away.
And if even one of these couriers could be identified and tracked consistently, the consequences could be enormous. Because a courier eventually has to reach his destination, but identifying them proved far more complicated than expected. Many couriers used false identities. They traveled through regions where records were limited or non-existent.
They blended into local populations where strangers rarely attracted attention and often even captured members of the organization knew very little about them. Some detainees could recall nicknames. Others remembered brief encounters with individuals who delivered messages and disappeared again.
But very few could provide real names or locations. The mystery grew deeper with every interview. Some prisoners spoke of a particular messenger trusted by senior leadership. Others mentioned a figure who carried instructions from high-ranking commanders, but whose identity remained carefully concealed. Occasionally, interrogators heard the same description repeated across separate interrogations conducted months or even years apart.
A quiet man, rarely speaking, delivering messages between individuals who never met directly. But the details were vague. Sometimes the name changed. Sometimes only a fragment of information remained. Yet the recurring references began to raise a question that intelligence officers could not ignore. What if this mysterious courier was more than just a messenger? What if he was the key to reaching the leadership itself? But even if that were true, another problem remained.
Finding one man in a region stretching across thousands of kilometers filled with mountains, deserts, cities, and villages was an almost impossible task. The intelligence community had satellites, surveillance aircraft, intercept technology capable of monitoring vast volumes of communication, but none of those systems could easily track a single individual traveling quietly along rural roads or remote trails.
To locate him would require patience, years of analysis, fragments of information gathered from completely unrelated investigations, and perhaps most importantly, a moment when the courier made a mistake. But mistakes are rare among individuals who understand they are being hunted. Which meant the intelligence effort would have to wait, watch, collect fragments, and slowly build a picture of a man who existed almost entirely in the shadows.
But what investigators did not yet realize was that this mysterious courier had already been mentioned several times within intelligence files. His name had appeared quietly during interrogations. It had surfaced inside captured documents. It had been whispered by detainees who knew they were speaking about someone important.
Yet, no one had recognized just how important he might be. Because sometimes the most critical clue in an investigation is not hidden. It is simply overlooked. And when analysts finally began to revisit those earlier reports, they discovered something unexpected. The same name had been appearing in intelligence records for years.
And that name might lead them closer to the most wanted man in the world. As analysts revisited years of scattered intelligence reports, a quiet realization began to take shape. The key to locating al-Qaeda’s leadership might not lie in technology or satellite imagery. It might lie in understanding how the organization itself survived.
Behind every clandestine network lies a set of unwritten rules, practical methods developed through years of experience operating under pressure. These methods are not written in manuals or official documents, but they shape every decision leaders make when they know they are being hunted. For al-Qaeda, survival depended on reducing exposure.
Every phone call could be intercepted. Every electronic message could be traced. Every known location could eventually be targeted. So, the leadership gradually adopted a doctrine of communication designed to leave as few detectable signals as possible. They eliminated speed. They eliminated convenience. They eliminated anything that relied on modern technology.
Instead, they returned to something far older human messengers. The logic behind this decision was brutally simple. A digital signal travels instantly, but it can be recorded, analyzed, and traced back to its origin. A courier, on the other hand, leaves almost nothing behind. No signal, no transmission, no electronic footprint, just a person moving through the landscape.
To intelligence systems designed to monitor communications, this was almost like silence. But silence created its own kind of structure because a courier system requires discipline. Messages must travel along trusted paths. Certain individuals must know where leaders are hiding. Certain routes must remain secure.
and only a very small number of people can be trusted to carry information between the highest levels of the organization. This structure was not unique to al-Qaeda. Throughout history, clandestine groups have relied on similar methods. Resistance movements during the Second World War used couriers to pass messages between occupied cities.
Cold War espionage networks often depended on intermediaries who carried information across borders. Even ancient military commanders relied on trusted messengers when written communication could not be secured. But the system has an inherent vulnerability. If a courier is discovered, the trail of his movements can reveal far more than the message he carries.
He can reveal who he meets, where he travels, which locations serve as communication hubs, and ultimately where the leadership might be hiding. Inside intelligence headquarters, analysts began mapping the possibility that al-Qaeda had built exactly this kind of courier network. They examined interrogation transcripts from detainees captured during operations in Afghanistan and Pakistan.
They reviewed intelligence collected years earlier, reports that had once seemed minor or incomplete. Certain references kept appearing. A courier trusted by senior leadership. a messenger who delivered instructions between isolated locations. A man whose identity remained carefully protected even within the organization.
At first, these references appeared inconsistent. Different detainees used different nicknames. Some described the courier as highly cautious, rarely speaking during meetings. Others remembered only brief glimpses, an individual arriving quietly, delivering a message, and leaving before questions could be asked.
But gradually the fragments aligned. Multiple interrogations conducted years apart and in different locations seemed to describe the same figure, the same quiet messenger, the same trusted intermediary between senior leaders, the same man whose identity few people seem to know.
And this is where the doctrine of secrecy within al-Qaeda began to reveal its unintended weakness. Because extreme secrecy limits the number of people who can carry critical information. And when only a few individuals hold that responsibility, those individuals become extremely valuable targets. If intelligence officers could identify even one of them, they might be able to follow the thread back to the center of the network.
But identifying the courier required more than speculation. Analysts needed something concrete. a name, a face, a location. For months, investigators combed through interrogation transcripts, searching for repeated references that might point to a real identity. Some detainees spoke of a man known only by a nickname. Others recalled fragments of his background, his region of origin, or the language he spoke.
But none of these details were precise enough to confirm who he was. And then buried deep inside earlier intelligence files, analysts found something interesting. Several detainees had mentioned the same alias. Not frequently, not clearly, but often enough that it began to stand out. The name referred to a courier believed to be trusted by members of al-Qaeda’s senior leadership.
At the time, the reference had seemed minor. Investigators had been focused on more prominent figures, commanders, planners, financiers. A courier had seemed less important. But now, with the benefit of years of analysis, that earlier dismissal began to look like a mistake. Because in a network built around secrecy, the courier might be the most important link of all.
Still, knowing an alias was not enough. Aliases change. Individuals adopt new identities. And in regions where records were limited, tracking someone based on a nickname alone could be nearly impossible. But analysts kept digging. They searched for any additional references connected to the alias. Travel patterns, associates, financial activity.
Occasionally, a small clue emerged, something that hinted the courier might originate from a particular region, or that he had connections to individuals already under observation. None of the clues were decisive, but they formed the beginnings of a trail. And if the trail could be followed long enough, it might lead somewhere extraordinary.
Because if the courier truly served the senior leadership of al-Qaeda, then sooner or later he would need to deliver a message to one of them. And that meant he would eventually have to travel to wherever they were hiding. But the intelligence officers pursuing this trail understood something else. Even if they found him, following him would be extremely dangerous.
The regions where he likely operated were filled with armed groups, tribal networks, and shifting alliances. Surveillance would have to be conducted carefully, quietly, and often from great distances. One mistake could alert the courier that he was being watched. And if that happened, the entire network might disappear again.
But the possibility was too important to ignore. Because somewhere in the shadows of that courier network was a path leading toward the most elusive target of the entire war, a man who had vanished after the attacks of September 11th. A man whose voice continued to appear in recordings even as his location remained unknown. A man whose survival symbolized the continued existence of the organization he had built.
And now, after years of searching, intelligence officers believed they might finally have discovered the method that could lead them to him. The investigation now revolved around a single idea. If the leadership of al-Qaeda had chosen to abandon electronic communication, then the entire organization depended on a small number of trusted couriers.
These individuals moved quietly across borders, carrying instructions that could not be transmitted through phones or radios. Somewhere among them was a messenger who might unknowingly lead intelligence officers directly to the heart of the network. But identifying that courier required turning fragments of information into something solid.
Inside intelligence centers, analysts began reconstructing every mention of the mysterious messenger that had appeared in earlier interrogations. Detainees captured during operations in Afghanistan, Pakistan, and other regions had occasionally referenced a courier trusted by senior leadership. Most had offered little detail.
Some remembered only a nickname. Others described a man who rarely spoke and whose movements were carefully concealed even from members of the organization. But when analysts compared these interviews side by side, a clearer pattern began to emerge. Multiple detainees referred to a courier known by a particular alias.
The name appeared in different interrogations conducted in different years, sometimes by prisoners who had never met each other. Each reference was vague, but the repetition suggested something important. This individual was not just another messenger. He was someone trusted by figures at the very top of the organization. And that meant finding him could change everything. But there was a problem.
The alias itself revealed almost nothing about his real identity. In regions where many individuals shared similar names and where official records were often incomplete, tracing a person through a nickname alone was extraordinarily difficult. Investigators needed more. So, the search expanded. Analysts began reviewing older intelligence reports that had once seemed unrelated.
They studied captured documents taken during raids on abandoned compounds. They examined travel records, financial transfers, and reports from human sources across multiple countries. Most of the information led nowhere. Weeks passed with no clear breakthrough. But the investigation continued because intelligence work often advances through persistence rather than sudden discovery.
And slowly, another clue began to surface. Some detainees had not only mentioned the courier’s alias, they had also hinted at where he might come from. Fragments of conversation suggested he might originate from a particular region of Pakistan. Other reports hinted that he had once served as a trusted assistant to a senior member of al-Qaeda.
Individually, these details seemed uncertain, but together they formed the beginnings of a profile. The courier was likely someone who had been connected to the organization for many years. He had earned enough trust to communicate directly with senior leaders. And he possessed the discipline required to operate under intense secrecy.
But there was still one enormous challenge. Even if investigators could determine his real name, finding him in the vast and complicated geography of South Asia would be extremely difficult. The region contained countless towns, villages, and remote communities. Borders were porous. Travel often occurred without official documentation.
And individuals accustomed to clandestine work were skilled at avoiding attention. But intelligence officers believed they had one advantage. Because even the most careful courier must eventually make contact with others. He must meet people, deliver messages, travel along routes that connect hidden locations.
And if those routes could be identified, surveillance might reveal where he was going. So analysts began constructing a network map centered around the suspected career. They studied anyone who might have interacted with him. Former associates, possible relatives, individuals who had once served alongside him in earlier phases of the organization.
Each connection became a potential doorway into his movements. But this process required extraordinary patience. Investigators were not looking for dramatic revelations. They were searching for tiny shifts in patterns, subtle changes that might reveal when the courier reappeared somewhere within the network.
Months turned into years. At times, the trail seemed to disappear completely. Yet, intelligence officers continued gathering fragments from across multiple investigations. And eventually, something important happened. A detainee provided information that helped analysts connect the courier’s alias to a real individual.
The name had appeared before, but earlier investigators had not realized its significance. Now, when placed alongside years of accumulated intelligence, it suddenly mattered because it allowed analysts to move beyond speculation. They were no longer searching for a shadow defined only by rumors and nicknames. They were searching for a specific person, but even with a name, the hunt remained extremely complex.
The courier operated cautiously. He rarely used telephones. He avoided predictable travel patterns, and he spent long periods completely invisible to intelligence collection. Yet, investigators believed the breakthrough was real. Because once an individual is identified, even partially, intelligence systems can begin looking for new traces.
Border crossings, vehicle registrations, associates who might unknowingly reveal his location. Slowly, the investigation shifted from theory to tracking. But the most important question remained unanswered. Where would the courier lead them? Because if he truly served the highest levels of al-Qaeda, then following him might reveal something that had remained hidden since the earliest days of the war.
The location of the organization’s most protected leaders. And somewhere along that hidden path was a destination that intelligence officers have been searching for since the attacks of September 11th. But before they could reach that destination, they would first have to find the courier himself. And that would prove to be far more difficult than anyone expected.
By the time intelligence analysts connected the courier’s alias to a real individual, the hunt had already stretched across several years. The attacks of September 11th had occurred long ago. Yet the most important leaders behind them remained hidden somewhere beyond the reach of conventional military operations. But now the investigation had changed.
For the first time, intelligence officers were no longer chasing only fragments of rumors and incomplete descriptions. They were searching for a specific person, an individual believed to serve as a trusted courier between members of Al-Qaeda’s senior leadership. Finding him became a priority shared across multiple intelligence agencies.
But the task was extraordinarily difficult. The courier understood the dangers of his role. Anyone trusted with carrying messages between senior figures of a clandestine organization would know that discovery could expose the entire network. So he operated with extreme caution.
He avoided telephones whenever possible. He used indirect travel routes and he often disappeared for long periods of time, leaving almost no trace that could be followed. This forced intelligence officers to adopt a strategy built on patience. They could not expect a single breakthrough that revealed everything at once. Instead, they would have to collect small pieces of information over time, observations that might seem meaningless individually, but could form a larger picture when combined.
The search expanded across multiple countries. Field officers worked with local intelligence services. Human sources were asked to report on individuals whose identities match the emerging profile of the courier. Analysts reviewed travel patterns and communications linked to people who might have crossed paths with him.
Every lead was examined. Most of them led nowhere. But intelligence investigations rarely move forward through dramatic discoveries. More often they progressed through long periods of quiet observation punctuated by small moments of clarity. And eventually one of those moments arrived. Information began to surface suggesting that the courier was still active.
He had not vanished after the early years of the war. Instead, he continued moving quietly between locations, maintaining the communication pathways that allowed the leadership of al-Qaeda to remain connected despite their isolation. This discovery was significant because it meant the courier was still performing the same role described in earlier interrogations, which meant that somewhere the leaders he served were still alive and receiving his messages.
But locating him required something more precise than scattered intelligence reports. Investigators needed to identify how he moved through the region, what routes he used, which vehicles he traveled in, and perhaps most importantly, where those journeys began and ended. Surveillance systems began focusing on individuals suspected of having contact with him.
In regions where reliable records were limited, intelligence officers relied heavily on human observation. Vehicles were noted. Movements between towns were tracked. Unusual patterns of travel were quietly recorded. None of this could happen quickly. The courier’s movements were irregular and unpredictable. Sometimes months would pass without any confirmed sighting.
At other times, fragments of information suggested he had briefly appeared in one location before disappearing again. But analysts believe that every movement, no matter how small, brought them closer to understanding his routine. And if they could understand a routine, they might eventually discover where he returned. But this stage of the operation required extraordinary discipline.
Following a courier connected to senior leadership meant operating under strict secrecy. If he ever suspected he was being watched, he could simply vanish. He could change identities, alter routes, or stop traveling entirely. Any one of those actions could break the trail permanently. So, intelligence officers avoided aggressive surveillance.
They watched from a distance. They gathered information slowly. They waited for the courier to reveal something about the network he served. And eventually, that patience began to pay off. Investigators started noticing a pattern in some of his movements. Certain journeys appeared to connect locations that had previously attracted little attention.
These were not the remote mountain hideouts many analysts had expected. Instead, some of the activity seemed to lead toward more populated areas. Cities where anonymity could be easier to maintain among thousands of ordinary residents. At first, this seemed unlikely. Many had assumed that senior leaders of al-Qaeda would hide in the most inaccessible regions available, deep inside mountains or remote villages far from government control.
But intelligence history often shows the opposite. Sometimes the safest hiding place is not the most isolated one. It is the place where no one thinks to look. This possibility forced analysts to reconsider their assumptions. If the courier was traveling to populated areas, then perhaps the leadership he served was not hiding in distant caves or isolated camps.
Perhaps they were living quietly somewhere far less obvious. But even that realization did not provide an exact location. It only suggested a new direction for the investigation, and the courier still remained elusive. His movements were rare, his appearances brief, his routes deliberately unpredictable. Yet every fragment of information added another line to the invisible map analysts were building.
A map that traced the pathways of a man whose journeys might eventually reveal the location of the most wanted terrorist leader in the world. But the final breakthrough had not yet arrived. Because somewhere along the courier’s route was a destination he visited repeatedly. A place that appeared ordinary from the outside.
A place that had existed quietly for years without attracting significant attention. And when intelligence officers finally began to focus on that location, they realized they might be looking at something far more important than anyone had imagined. By the time analysts began narrowing their focus toward the courier’s movements, the intelligence effort had evolved into something far more precise than it had been in the early years after the attacks.
At the beginning of the campaign, the objective had been broad. Disrupt the network, capture operatives, collect information wherever it could be found. Now the mission had become something different. Everything centered on a single thread. Follow the courier. Because if the assumptions were correct, that thread might lead directly to the hidden core of al-Qaeda’s leadership.
The breakthrough did not arrive as a dramatic revelation. It began with a pattern that slowly became impossible to ignore. Fragments of surveillance, human reporting, and travel observations began pointing toward a specific route the courier appeared to use more than once. His journeys were still irregular, carefully spaced apart, but certain destinations seemed to reappear in the intelligence record.
One of those destinations stood out, a city in Pakistan that on the surface appeared completely ordinary. It was not a remote mountain fortress. It was not a militant stronghold deep inside tribal territory. It was a populated urban area, busy, crowded, and filled with ordinary neighborhoods where thousands of families lived their daily lives.
At first, this seemed counterintuitive. For years, many analysts had assumed that the most senior figures of al-Qaeda would hide in remote terrain where surveillance aircraft and government forces would struggle to reach them. But the courier’s movement suggested something very different. He appeared to travel toward a settled area where militarymies, residential streets, and markets existed side by side.
This forced investigators to confront an uncomfortable possibility. Perhaps the leadership of the organization had chosen to hide somewhere that seemed almost too ordinary to attract suspicion. The idea was not unprecedented. Throughout history, individuals attempting to avoid detection had often hidden in places that appeared completely normal.
Remote locations invite scrutiny, but ordinary neighborhoods rarely do, and this is where the intelligence effort began to sharpen its focus. Surveillance assets were directed toward observing locations associated with the courier’s movements. Vehicles were noted, routes were monitored, and eventually analysts noticed something unusual.
The courier appeared to visit a particular compound on the outskirts of the city. From above, the structure did not resemble a typical residence. It was surrounded by unusually high walls. The buildings inside the compound were larger than those in neighboring houses. And unlike most homes in the area, the property seemed deliberately designed to limit visibility from the outside.
Even more unusual was the behavior observed there. The residents rarely left the compound. There were no obvious internet connections or phone lines linking the property to outside networks. Trash was reportedly handled in an unusual way, burned rather than placed outside for collection. At first, none of these details proved anything.
Unusual buildings exist everywhere. Families sometimes prefer privacy, and intelligence officers knew better than to jump to conclusions based on limited observations. But the pattern of the courier’s visits continued. He returned to the same compound more than once. And each time he appeared there, investigators were reminded of the central question that had guided the search for years.
Who was he delivering messages to? Inside intelligence centers, analysts debated the possibilities. Some believed the compound might house a mid-level facilitator, someone responsible for coordinating communication between scattered parts of the network. Others wondered whether it might shelter several members of the organization who had chosen to live quietly under assumed identities.
But a smaller group of analysts began to consider a far more extraordinary possibility. What if the courier’s destination was not just another member of the network? What if it was someone far more important? The compound itself offered clues that deepened the mystery. Its construction was unusual for the surrounding neighborhood.
The walls were higher than typical residential boundaries. There were security features that seemed excessive for an ordinary home. Yet, the property did not resemble a military facility or fortified compound. It sat quietly among other buildings, attracting little attention from the outside world. But the behavior of its occupants raised questions.
No one inside appeared to travel frequently. Visitors were rare, and yet the compound’s residents seemed to maintain strict isolation. For intelligence analysts, these details triggered a familiar instinct. Secrecy of that level usually exists for a reason, but confirming what that reason might be proved extremely difficult.
Direct surveillance of the compound carried enormous risk. If the occupants became aware they were being watched, they could disappear overnight. And if the individual inside truly was connected to the senior leadership of al-Qaeda, that disappearance could erase the most promising lead the intelligence community had discovered in years.
So the investigation proceeded carefully. Analysts gathered more imagery. They studied the compound’s layout. They examined every movement connected to the courier’s visits. But despite months of observation, one crucial detail remained missing. No clear visual confirmation of who lived inside.
From the outside, the compound revealed almost nothing. Its walls blocked direct views of the interior. The residents avoided exposure, and no identifiable communications connected the property to known figures within the organization. Yet, the pattern of the courier’s visits remained impossible to ignore. Each time he appeared at the compound, the possibility grew stronger that this quiet location might hold something extraordinary.
But even as that suspicion deepened, intelligence officers faced a difficult question. Observation alone could not solve the mystery. Eventually, someone would have to decide whether the compound was important enough to justify action. Because if the analysts were correct, and the courier had been leading them towards something hidden inside those walls, then the quiet property in that ordinary city might contain the most significant target of the entire war and confirming that possibility would require moving beyond
surveillance. It would require a decision that carried enormous consequences. By the time the compound had been under quiet observation for months, the investigation had reached a point where analysis alone could no longer provide answers. For nearly a decade, intelligence officers had been searching for the leadership of al-Qaeda.
Thousands of reports had been written. Countless leads had appeared and disappeared. Yet now, for the first time since the early days of the war, analysts believed they might be close to something real. But belief was not proof. Inside intelligence headquarters, teams of analysts studied every available detail about the compound.
Satellite imagery revealed the layout of the buildings. Surveillance reports documented the courier’s movements. Intelligence officers examined construction records and property histories in an attempt to understand when the compound had been built and who might have financed it. What they discovered only deepened the mystery.
The compound had been constructed several years earlier, yet its design did not resemble typical houses in the surrounding neighborhood. The outer walls were unusually high. Barbed wire lined portions of the perimeter. The main building inside the compound stood taller than most nearby structures, offering a vantage point over the surrounding streets.
But what attracted the most attention was the behavior of its occupants. The residents rarely left the property. When they did appear briefly outside, they avoided contact with neighbors. No vehicles seemed permanently associated with the compound, even though a property of that size would normally house several families.
Even more unusual, there were no visible telephone lines or internet connections leading into the building. In a modern urban environment, that absence stood out. Inside intelligence briefings, these details were examined again and again. None of them proved who lived there, but together they suggested something unusual was happening behind those walls.
Some analysts began asking a question that once would have seemed almost impossible. What if the courier had been visiting someone far more important than anyone initially imagined? What if the compound sheltered a senior leader of al-Qaeda? Perhaps even the most senior of them all. But this possibility carried enormous weight because if the person inside the compound truly was the leader of the organization responsible for the attacks of September 11th, then confirming his presence would become one of the most significant intelligence discoveries in
modern history. Yet confirmation remained elusive. No direct imagery revealed the face of anyone inside the compound. No intercepted communication linked the location to known members of the network. The residents maintained strict isolation, rarely appearing outside the walls.
Analysts had only indirect clues, the courier’s visits, the compound’s unusual security features, the absence of electronic communication, and the quiet behavior of the individuals living there. Each clue alone could be explained in ordinary ways, but taken together, they formed a pattern that was difficult to dismiss. Inside intelligence circles, the compound became the focus of intense debate.
Some analysts believed the evidence was strong enough to justify action. Others urged caution. Launching an operation based on incomplete information could have serious consequences. If the compound turned out to house someone else entirely, the political and strategic fallout could be significant. And even if the target truly was hiding there, the risks of an operation would be enormous.
The compound was located in a populated city. Any military action carried the possibility of drawing attention from local authorities, nearby residents, or armed groups operating in the region. The planning would have to be precise, careful, quiet. But the alternative, doing nothing, carried its own risk. Because if the individual inside the compound truly was the leader of al-Qaeda, every day that passed allowed him to remain hidden.
For intelligence officers who had spent years pursuing this investigation, the decision was becoming unavoidable. Observation alone could not answer the final question. Sooner or later, someone would have to determine whether the compound contained the most wanted terrorist leader in the world. The debate eventually reached the highest levels of government.
Briefings were prepared. Evidence was presented. Satellite images, intelligence reports, and analytical assessments were reviewed again and again. Even then, uncertainty remained. No one could say with absolute certainty who lived behind the compound’s walls, but the pattern of evidence pointed toward a possibility too important to ignore.
Because if the analysts were right, the quiet property at the edge of that city was not just another house. It was the hiding place of a man who had evaded capture for nearly a decade. And if that was true, the next step would not be another round of analysis. The next step would be an operation, an operation that would unfold in darkness, an operation designed to enter the compound without warning.
And inside those walls, the final answer to years of searching would finally be revealed. For nearly 10 years after the attacks of September 11th, the search had moved across continents. Intelligence teams had followed fragments of communication across mountains, deserts, and cities. Military units had captured operatives, dismantled training camps, and gathered thousands of pieces of information scattered across countless investigations.
Yet the central figure behind the attacks had remained hidden. Now the search had narrowed to a single compound, a quiet property surrounded by high walls, a place that from the outside looked like just another residence in an ordinary neighborhood. But behind those walls, analysts believed something extraordinary might be unfolding.
The evidence was never perfect. No satellite image revealed the identity of the man inside. No intercepted call confirmed his presence. The intelligence case had been built slowly, piece by piece, through patterns rather than certainty, the courier’s repeated visits, the unusual design of the compound, the deliberate absence of electronic communication, the isolated behavior of the people living there.
Individually, each detail meant little. Together, they pointed toward a possibility that had once seemed almost impossible. that the leader of al-Qaeda had not been hiding deep inside remote mountains as many had believed. Instead, he might have been living quietly inside a walled compound in the middle of a populated city.
But intelligence work often operates in the realm of uncertainty. Even after months of surveillance, analysts could not say with complete confidence who lived there. They could only say that the pattern of evidence pointed in one direction. And eventually, the question became unavoidable. How long could they wait? Because every day that passed carried its own risks.
If the courier changed routes, the trail might vanish again. If the occupants of the compound became suspicious, they could disappear overnight. Years of investigation could collapse instantly. So the moment arrived when analysis had to give way to action. Planning began for an operation designed to answer the question once and for all.
The mission would be conducted at night. It would rely on speed, surprise, and secrecy. The objective was simple. Enter the compound, identify the individuals inside, and confirm whether the most wanted terrorist leader in the world had finally been found. But even as preparations moved forward, uncertainty remained.
Intelligence officers knew that operations based on incomplete information always carried risks. The compound might contain someone else entirely. The target might not even be there. Yet, the possibility was too significant to ignore. Because if the analysts were right, this single location could resolve one of the longest and most complex intelligence hunts in modern history.
And so, under the cover of darkness, aircraft carrying a specialized team moved quietly toward the city. The operation itself would unfold quickly, but its significance extended far beyond that single night because the discovery of the compound had revealed something larger than the location of a single individual. It demonstrated how intelligence operations evolve over time.
The search had not succeeded through technology alone. Satellites, surveillance aircraft, and digital monitoring had provided valuable information, but they had not solved the mystery. The breakthrough had come from understanding the human structure of the network. From recognizing that an organization trying to avoid electronic surveillance must rely on trusted couriers.
From patiently following one of those couriers across years of fragmented intelligence. That realization had turned a nearly invisible network into something that could finally be traced. The courier had not intended to reveal anything. He had simply continued performing the role the organization required. carrying messages, maintaining connections, moving quietly between locations that no one outside the network was supposed to understand.
But every journey left a trace. And over time, those traces formed a path. A path that led investigators to a single compound hidden in plain sight. The story of that investigation reveals something fundamental about modern intelligence work. It is rarely the result of one dramatic discovery. More often, it is the result of patience.
Years of collecting small fragments of information. Years of analyzing patterns that only become meaningful when seen together. In the end, the operation that followed would become one of the most well-known moments in the global fight against terrorism. But the operation itself was only the final step. The real story had begun years earlier.
inside quiet intelligence rooms where analysts examined scattered clues and asked a simple question. If the leaders of al-Qaeda had disappeared, how were they still communicating? The answer to that question led investigators to a courier. And following that, Courier ultimately revealed the hidden place where the long search finally reached its conclusion.
A search that had begun in the chaos of September 2001 and ended nearly a decade later with a single discovery behind the walls of an ordinary compound.
News
How A Stairs Of Death Execution Worked
During the Second World War, the Mount Housen concentration camp in Austria became one of the most notorious and brutal of all the Nazi camps. Perched on a hill above the small town of Mount Housen, it was built near…
What American Soldiers Saw on the “Stairs of Death” at Mauthausen
May 5th, 1945. Upper Austria. The US 11th Armored Division was moving through the beautiful Danube Valley. The war was practically over. But as the American tanks crested a hill near the town of Montousen, they saw something that looked…
Painful Execution of Nazi Sexual Deviant & Fanatical Anti-Semite: Julius Streicher
The 1st of October 1946, Nuremberg, Germany. After more than 10 months on a trial, 21 defendants who are among the most important political, military, and economic leaders of Nazi Germany, hear their sentences read. These high-ranking representatives of the…
The Fate of Hermann Göring’s Family After the Fall of Nazi Germany
On the night of 15 October 1946, Hermann Göring ended his life in his Nuremberg cell, just hours before his scheduled execution. His death closed his chapter in history, but it opened another one: what happened to the…
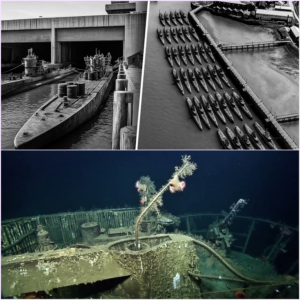
What Happened to the German U-Boats After WW2?
When Nazi Germany surrendered in May 1945, more than a hundred U-boats were still at sea. In the days that followed, they surfaced in quiet harbours across Europe, their war finally over.What came next was unprecedented: hundreds of…
She Was Looking for Kristofferson. Found LEONARD COHEN. He Wrote a Song
In 1968, Leonard Cohen stepped into an elevator at the Chelsea Hotel in New York and found Janice Joplain standing there. She told him she was looking for Chris Kristofferson. Cohen said he was Kristofferson. They both knew it was…
End of content
No more pages to load